I. The Institutional Perimeter
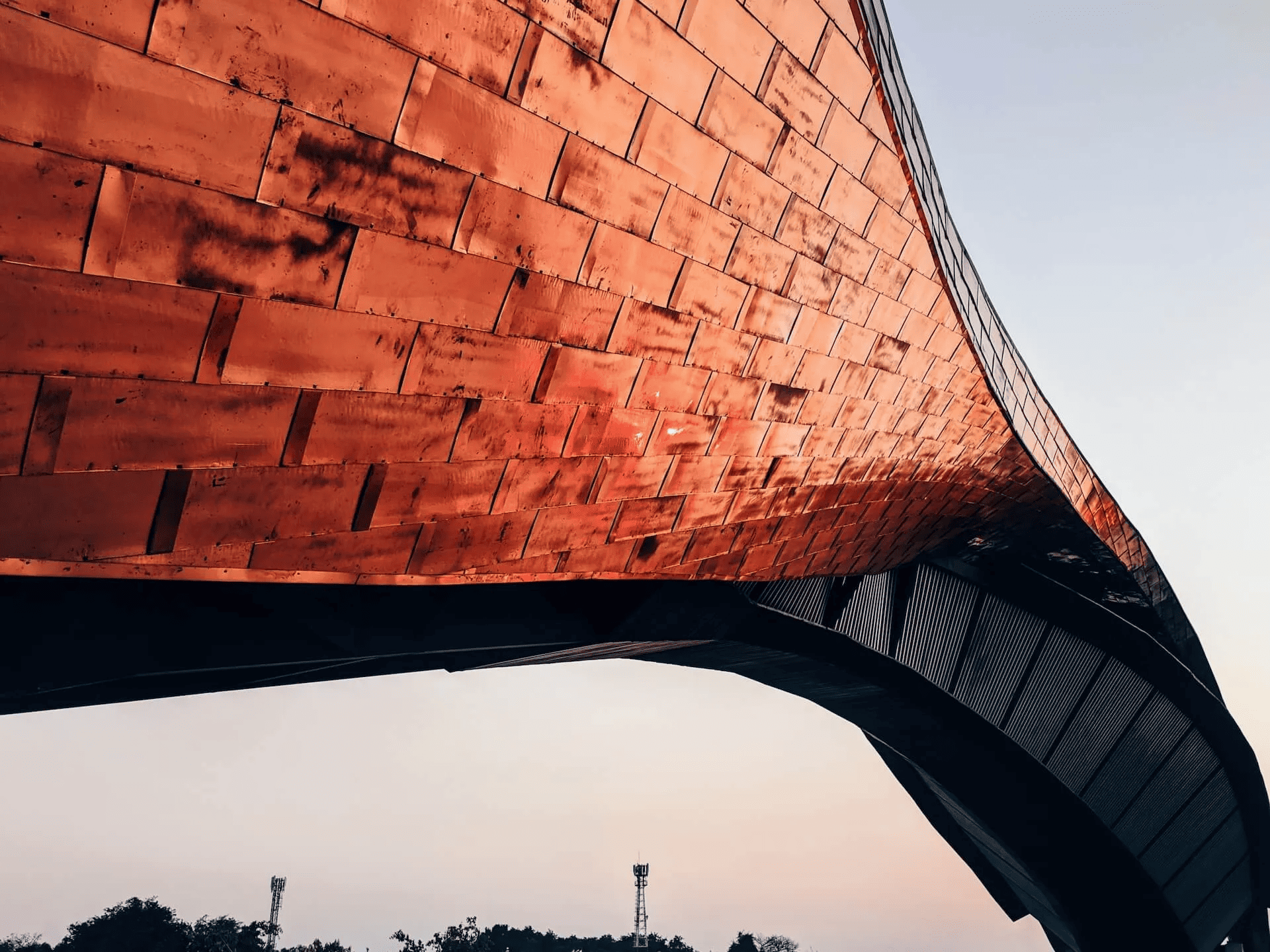
For five decades, the "Montclair Standard" has been synonymous with the secure custody of assets. Today, that custody extends into the digital realm. Our fraud prevention strategy is not a static set of rules, but a dynamic intelligence operation. We utilize a "Zero-Trust" architecture, ensuring that every transaction, communication, and access request is rigorously verified through multiple independent channels.
Our Zurich-based Security Operations Center (SOC) monitors global financial movements 24/7, utilizing proprietary pattern-recognition algorithms to identify anomalies before they manifest as risks.
II. Multi-Layered Authentication Protocols
Sovereignty Through Verification
Access to the Montclair ecosystem is protected by a hierarchy of authentication measures tailored to the complexity of your mandate:
- Biometric Identity Anchoring: Utilizing advanced physiological markers to ensure that only the verified Principal can authorize significant movement of capital.
- Hardware-Based Security Keys: We provide our clients with institutional-grade physical security tokens, isolating access credentials from the vulnerabilities of the public internet.
- Out-of-Band Verification: High-value transactions require a secondary, independent confirmation via a secure voice-link with your dedicated Client Advisor.
III. Common Threat Vectors & Countermeasures
Sophisticated fraud often targets the human element of the financial relationship. We maintain a high state of readiness against the following vectors:
How do we neutralize 'Social Engineering' and Phishing?
Fraudsters often impersonate bank officials to gain sensitive data. Crucial: Montclair Private Bank will never ask for your full password, PIN, or security tokens via email or telephone. All official digital communication is conducted exclusively through the encrypted Montclair Private Portal. If you receive an unsolicited request for information, it should be treated as a threat and reported immediately to your Advisor.
What is the 'Authorized Push Payment' (APP) Defense?
This occurs when a client is manipulated into authorizing a payment to a fraudulent account. To counter this, Montclair employs a "Verification of Payee" system and enforced "Cooling-Off" periods for first-time transfers to new jurisdictions or entities, allowing our compliance team to verify the legitimacy of the recipient.
How do we protect against 'Executive Impersonation'?
For Family Offices and Corporate entities, we mitigate "CEO Fraud" by requiring pre-established signatory matrices. No single individual can authorize the movement of significant funds without a dual-signature protocol verified by the bank's independent treasury desk.
IV. Cyber-Sanctuary: Protecting the Digital Footprint
In addition to institutional measures, we recommend our clients adopt a "Fortress Mindset" regarding their personal technology:
- Network Sovereignty: Avoid accessing the Montclair Private Portal via public or unsecured Wi-Fi networks. Utilize a dedicated VPN or a private, secured line.
- Device Hygiene: Ensure all terminals used for financial transactions are equipped with the latest security patches and are not shared with unauthorized personnel.
- Communication Discipline: Utilize encrypted messaging platforms for discussing sensitive financial matters with your advisory team.
V. Incident Response & Recovery
Time is the critical factor in asset recovery. If you suspect that your credentials have been compromised or you notice an unauthorized entry in your ledger:
- Immediate Suspension: Contact the 24/7 Montclair Emergency Security Line at +41 44 211 99 88 to freeze all account activity.
- Forensic Audit: Our cybersecurity team will conduct a thorough audit of your digital session to identify the breach point.
- Credential Reset: We will facilitate a total reset of your security parameters through a secure, in-person or verified video-link protocol.
VI. The Fiduciary Guarantee
At Montclair, we believe that the security of your capital is inseparable from the success of your legacy. We continuously invest in emerging technologies—from machine learning to quantum-resistant encryption—to ensure that our defensive perimeter remains unassailable. Your peace of mind is our primary objective.